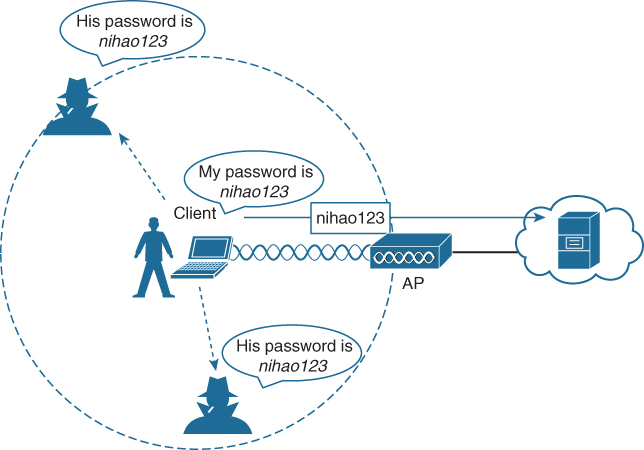
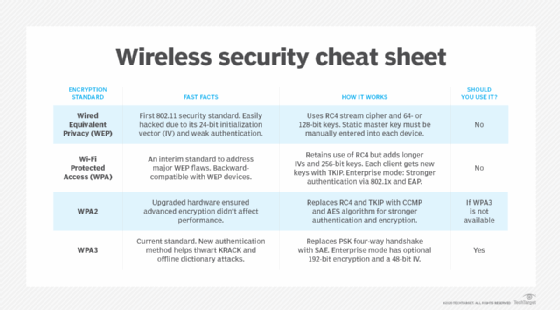
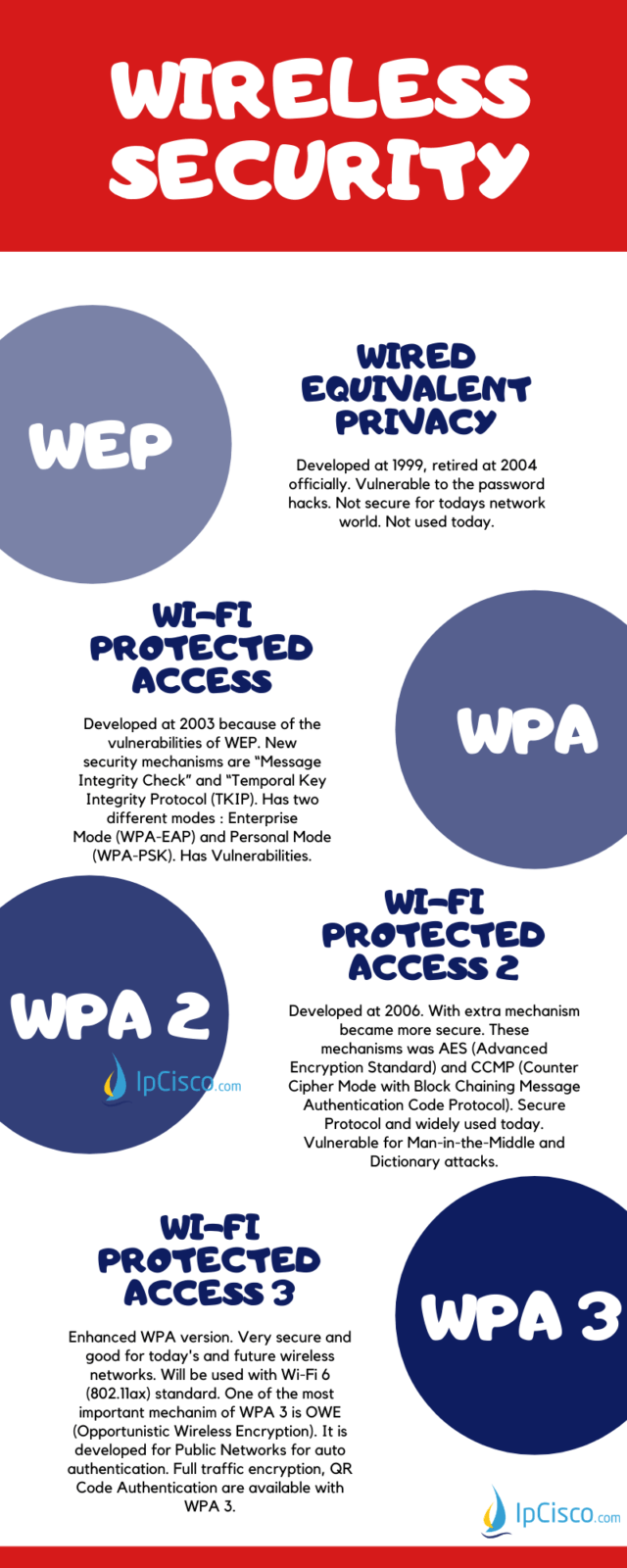
Wireless security protocols: The difference between WEP, WPA, WPA2 | Wireless security, Wireless networking, Wireless access points

Wi-Fi Wireless Password Security Protocols | In this video we will see about wireless password security options. Understanding different type of security modes - WEP, WPA, WPA2, WPA3, WPS, and... | By
Wireless Security Protocols Ppt Powerpoint Presentation Infographic Template Sample Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

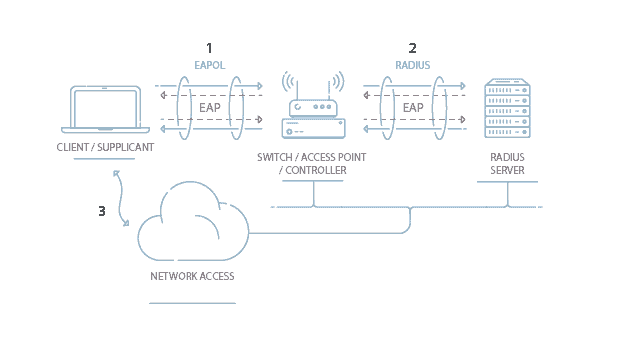

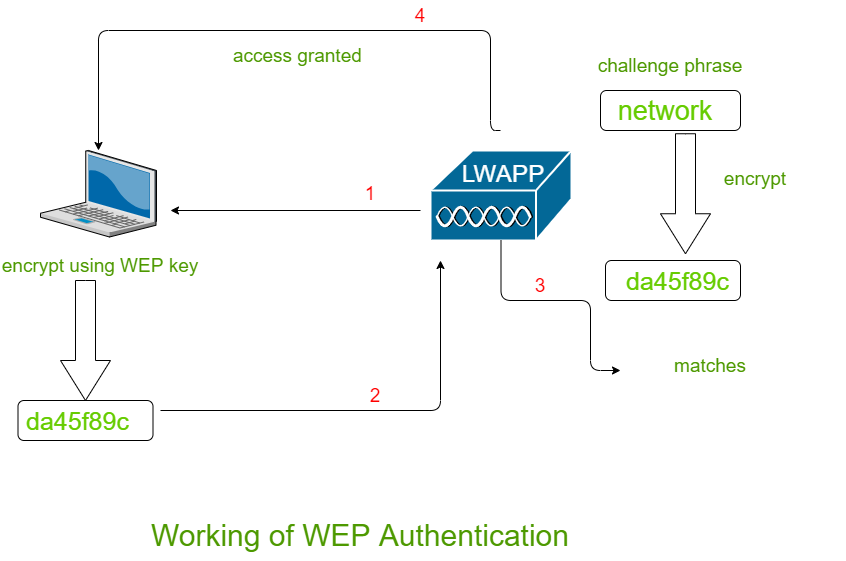









![PDF] Evolution of wireless LAN security architecture to IEEE 802.11i (WPA2) | Semantic Scholar PDF] Evolution of wireless LAN security architecture to IEEE 802.11i (WPA2) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/bf29313d67443446fad089ad590fea4570f70788/5-Figure4-1.png)